Crypto network vulnerabilities remain at large in 2023 after a disastrous 2022. In the latest example, a security research team revealed massive risks at DogecoinLitecoin, with developers warning of additional risks.
Cryptocurrencies use an open-source codebase designed to allow anyone to inspect, modify, and distribute the software’s source code. This openness promotes transparency, accountability, and innovation, enabling the crypto community to continually develop and improve blockchain technology.
However, it also means that the code is vulnerable to exploitation by malicious actors who can identify and exploit its weaknesses.
Different Ways Bad Actors Can Penetrate Network
Here are some ways in which open-source codebase can have vulnerabilities that could affect the security of the blockchain.
- Coding errors: Even the most experienced developers can make coding errors that could leave the code open to exploitation. For instance, a developer might create a vulnerability by failing to perform proper input validation, making it possible for an attacker to inject malicious code into the system. Similarly, an error in memory allocation or data handling could cause data corruption or leaks.
- Lack of code review: Open-source codebases rely on peer reviews to identify and fix issues in the code. However, if the codebase lacks a rigorous review process, it can lead to security gaps that attackers can exploit. Additionally, inexperienced developers who make changes without fully understanding the implications of their modifications can introduce new vulnerabilities.
- Forked code: Forking is a process in which developers change an existing codebase to create a new project. Although forking is expected in the open-source community, it can introduce vulnerabilities if the developers fail to incorporate security updates or make improper changes. If a forked project becomes popular, attackers may target it due to its potential vulnerabilities.
- Software dependencies: Many open-source projects function correctly using third-party libraries and frameworks. While these dependencies can save time and effort, they can also introduce vulnerabilities if they contain flaws or are outdated. Attackers can exploit these vulnerabilities to access sensitive data or compromise the blockchain’s integrity.
- Social engineering: Even if the codebase is technically sound, attackers can still exploit human weaknesses to access the system. For example, they might use phishing attacks to obtain login credentials or trick developers into introducing malicious code into the system.
Crypto Platforms See Rise in Illicit Activities
In conclusion, the open-source nature of crypto coins’ codebase provides significant benefits, such as transparency and innovation. However, it also introduces potential vulnerabilities that attackers can exploit. Therefore, developers must continually review and improve the code to ensure its security and maintain the blockchain’s integrity.
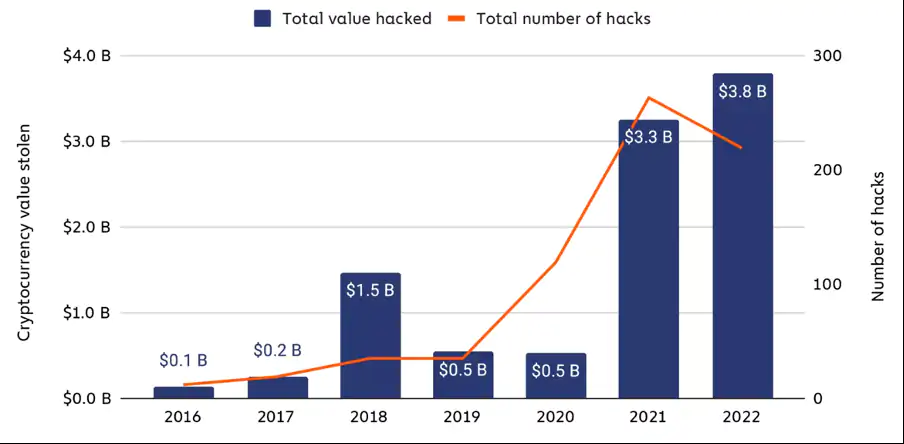
Bad actors involved in cryptocurrency hacks by $3.80 billion last year. Illicit activities in 2022 were up 15% on 2021 figures ($3.30 billion) and dramatically up on the $0.50 billion stolen in 2020.
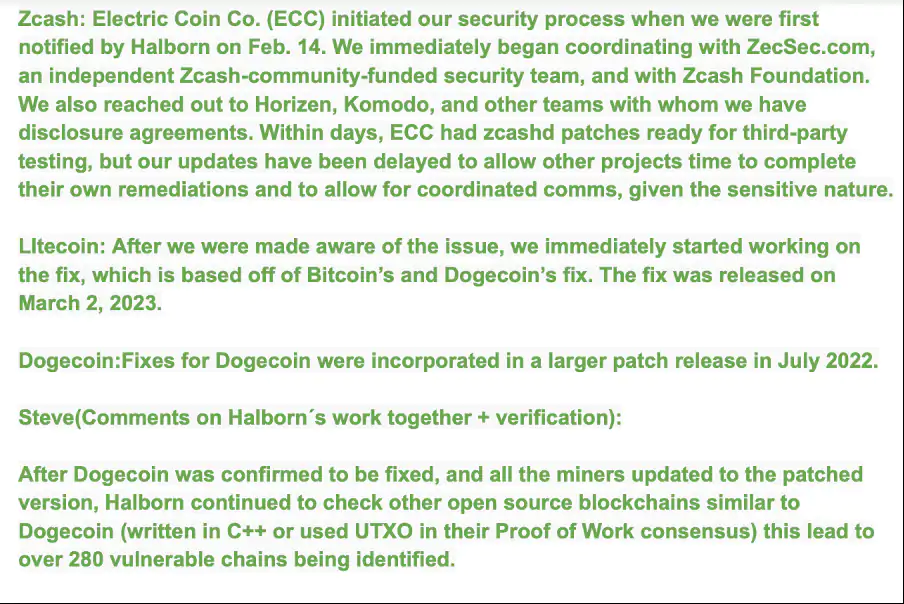
According to a finding from the cybersecurity firm Halborn, 2023 could have been even more disastrous. Vulnerabilities were discovered in over 280 major blockchains. These included Dogecoin, Litecoin, and Zcash. In total, about $25 billion of assets were put at risk.
?? Halborn discovered massive #ZeroDay impacting Dogecoin and 280+ networks including Litecoin and Zcash, putting over $25 Billion of digital assets at risk!
— Halborn (@HalbornSecurity) March 13, 2023
Highlighting the Main Loophole
Halborn researchers evaluated DOGE’s open-source code base to test for unknown exploits, or “zero-day vulnerabilities,” in its code that could target blockchain miners’ funds.
Researchers identified two critical gaps code-named Rab13s. The Dogecoin developers later solved the errors after being alerted by the security firm.
4/ Another zero-day identified by Halborn was uniquely related to #Dogecoin, including an RPC vulnerability impacting individual miners.
Subsequently, variants of these 0-days were also discovered in similar blockchain networks potentially leading to DoS or RCE attacks.
— Halborn (@HalbornSecurity) March 13, 2023
Severe Consequences of Malicious Events
Identifying loopholes raised more doubts as variants of these zero-days were also discovered in similar blockchain networks, including Litecoin and Zcash. Keeping the gaps in mind could lead to severe consequences.
Firstly, concerning the P2P messaging mechanisms, malicious consensus messages can be sent to each , causing them to shut down and exposing the network to severe risks like 51% attacks. Moving on, attackers can execute code through the public interface (RPC) as a normal node user. The likelihood of an exploit is lower since a valid credential is required to carry out the attack.
Therefore, to prevent further damage, the team at the security firm recommended upgrading all UTXO-based nodes (e.g., Dogecoin) to the latest version (1.14.6).
In a further conversation over the mail, the security firm answered a few questions asked by BeInCrypto. When asked about how Zcash, Litecoin, and Dogecoin fixed the vulnerabilities, the team replied:
Such incidents can have implications for the broader crypto ecosystem. Steve Walbroehl, the chief security officer and co-founder of Halborn, asserted:
“The longer the issues exist on public mainnets, the more likely it is found and exploited by hackers with malicious intentions. Since we had already finished the work with Dogecoin, we had the largest stakeholder already identify a solution and fix that could be given as an example for all the other chains. It was an honorable call to action for a positive outcome with disparate projects working to help each other solve a common threat.”
BeInCrypto contacted core developers at Dogecoin and Zcash for comments regarding this topic. However, hasn’t received a response yet.



